Cybersecurity as Physical Safety: Protecting Critical Infrastructure from Digital Threats
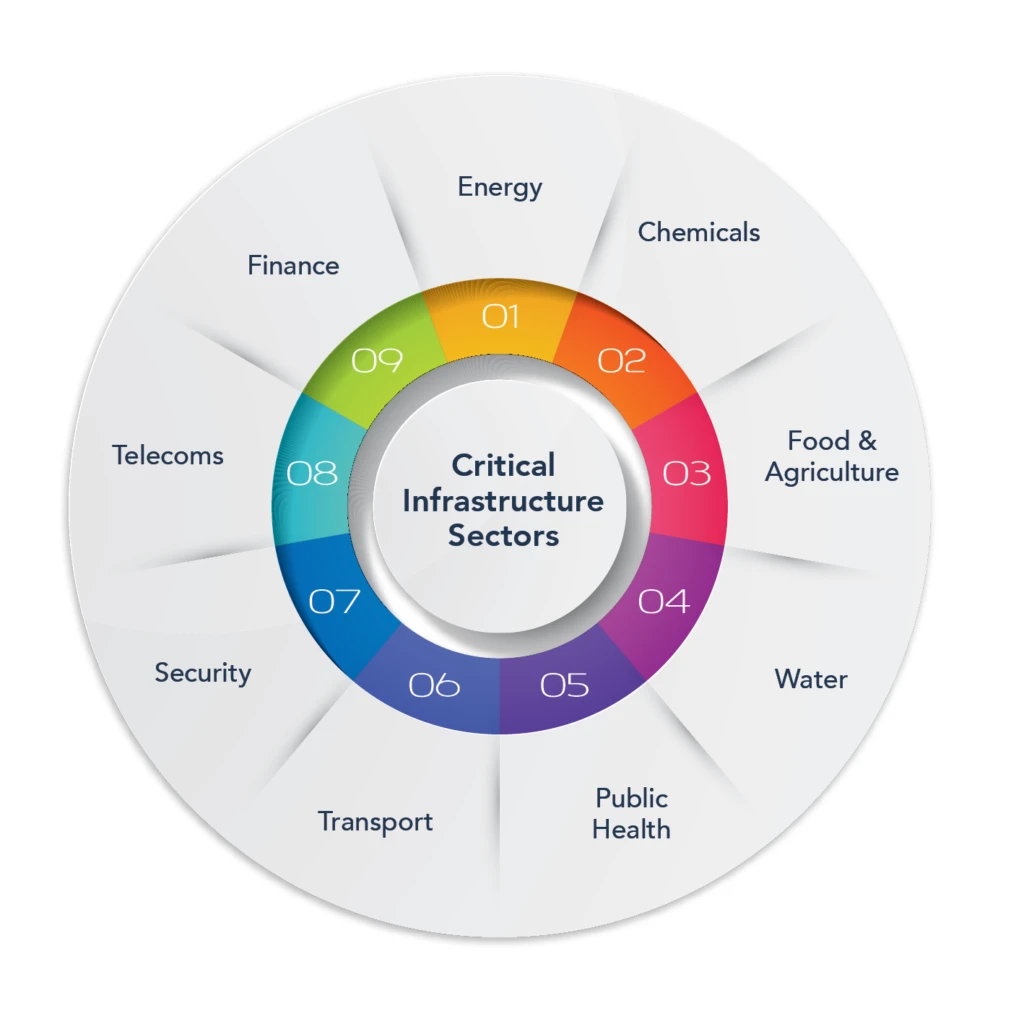
As critical infrastructure integrates with digital networks, cyberattacks now pose direct risks to physical safety, including power outages and water contamination. To mitigate these threats, industries are adopting Zero Trust architectures, network segmentation, and Digital Twins to simulate and defend against attacks. In this new era, cybersecurity is a fundamental pillar of public health and national safety.
For decades, the worlds of "bits" (digital data) and "atoms" (physical reality) were separate. A computer crash might lose you a spreadsheet, but it wouldn't stop a city’s water flow or cause a power plant to overheat. Today, that separation has vanished. As our power grids, water systems, and transportation networks become increasingly "smart" and interconnected, cybersecurity has officially become a matter of physical safety.
In 2026, a "breach" is no longer just about stolen passwords—it’s about protecting the systems that underpin human life.
The Convergence of IT and OT
The heart of our critical infrastructure lies in Operational Technology (OT). These are the hardware and software systems—such as SCADA (Supervisory Control and Data Acquisition)—that monitor and control physical processes like pressure in a pipeline or the voltage on a power line.
Historically, OT systems were "air-gapped" (physically disconnected from the internet). However, to improve efficiency, these systems have been integrated with corporate Information Technology (IT) networks. This connectivity has created a massive "attack surface."
Digital Threats with Physical Consequences
When a cyberattack targets critical infrastructure, the goal is often disruption rather than theft. The physical ramifications can be catastrophic:
Water Contamination: In 2021, a hacker famously accessed a water treatment plant in Oldsmar, Florida, attempting to increase lye levels to dangerous concentrations. While an operator caught the change in time, it highlighted how a few keystrokes could poison a community.
Grid Instability: Attacks on power grids, such as those seen in Ukraine, demonstrate that hackers can remotely open circuit breakers, plunging hundreds of thousands of people into darkness and disabling the heating systems and hospital equipment they rely on.
Kinetic Damage: By manipulating the logic of a machine (like a turbine or a centrifuge), attackers can force equipment to operate outside of safety parameters, leading to physical explosions, fires, or permanent mechanical failure.
Frameworks for Protection: The 2026 Strategy
To defend against these sophisticated threats, industries are moving beyond simple firewalls toward a Resilience-First model.
1. Zero Trust for Industrial Reality
The "Zero Trust" model operates on a simple principle: Never trust, always verify. In an industrial setting, this means that every device, user, and command—even those coming from inside the building—must be authenticated. This prevents an attacker who has stolen a single password from moving "laterally" through the system to reach the core controls.
2. Network Segmentation
By dividing a network into smaller, isolated zones (micro-segmentation), engineers ensure that a breach in the office's "guest Wi-Fi" cannot reach the "boiler control" system. This "containment" strategy is essential for protecting legacy equipment that wasn't originally designed with security in mind.
3. Digital Twin Simulations
Organizations are now using Digital Twins—virtual replicas of their physical infrastructure—to act as "cyber ranges." Security teams can simulate a cyberattack on the virtual power plant to see how it reacts, allowing them to patch vulnerabilities and rehearse emergency protocols without ever risking a real-world outage.
Conclusion: A Shared Responsibility
Protecting our infrastructure is no longer just the job of the IT department. It requires a unified front between engineers who understand the physical machines and cybersecurity experts who understand the digital threats. As the line between the digital and physical worlds continues to blur, our definition of safety must evolve to ensure that the systems we depend on for survival remain unshakeable.
